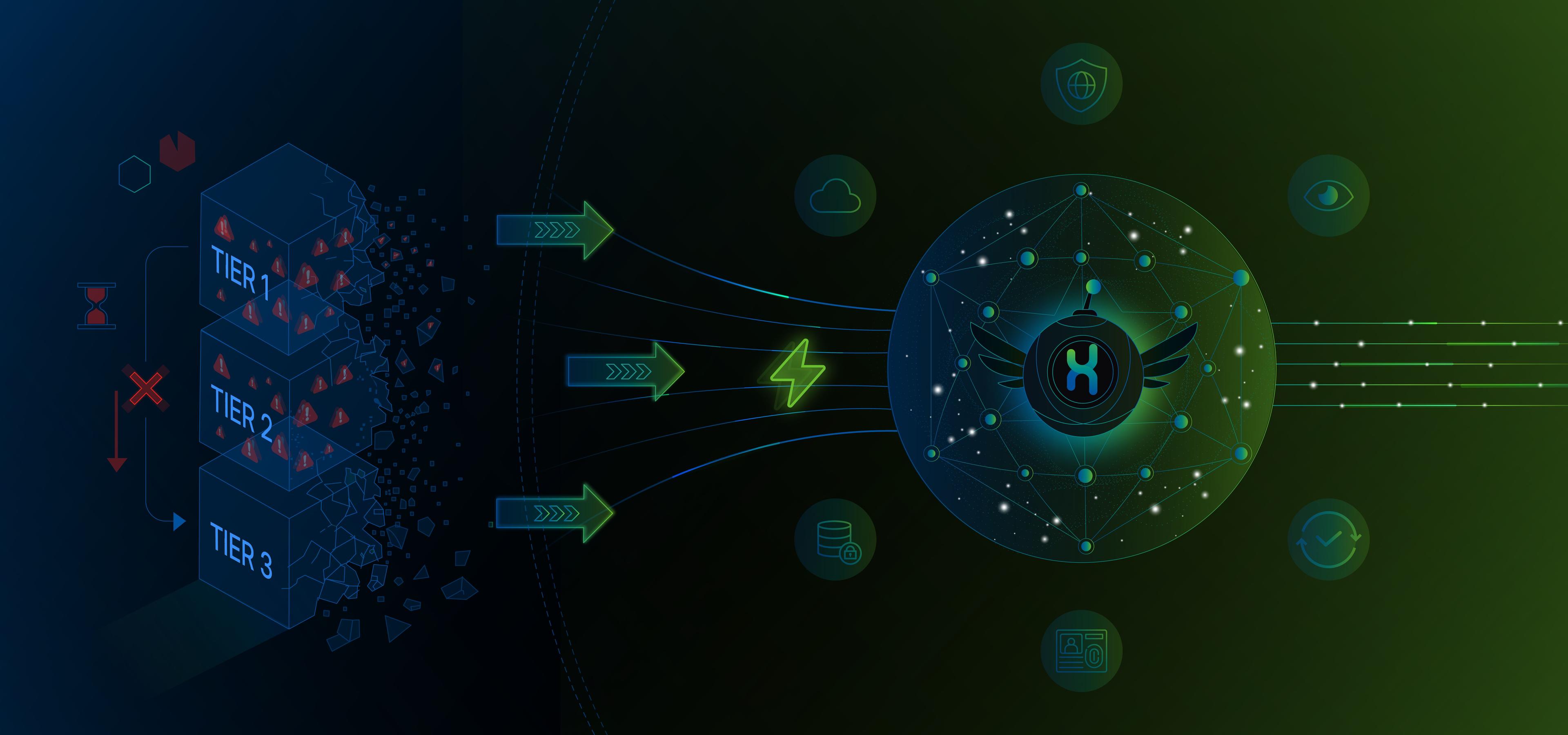
The Death of Tiers: Rethinking the SOC Architecture for the Agentic Era
How machine-speed adversaries are exposing the limits of tiered SOCs, and why agentic architecture is the way forward.

The Breaking Point of the Assembly Line
A breach does not wait for Tier 2.
Why does your SOC?
For more than two decades, SOCs have followed a model borrowed from the Industrial Revolution: the assembly line. Tier 1 triages. Tier 2 investigates. Tier 3 hunts. Each handoff introduces delay, and scale is achieved by adding more analysts.
That model assumed human effort could scale linearly with threat volume. It no longer can.
Modern adversaries operate at machine speed. Leveraging automation, they can move from initial compromise to lateral movement in under 60 minutes, often in mere seconds. Meanwhile, the tiered SOC is still routing tickets between queues.
The problem is not talent. It is architecture.
Every handoff introduces latency. Every manual correlation slows detection and response. While analysts review alert queues, attackers map permission paths, chain misconfigurations, and escalate privileges automatically.
We are attempting to fight algorithmic speed with administrative process.
The result is structural: the threat landscape is accelerating faster than our operating model can observe it. To remain viable, CISOs must dismantle the assembly line and replace it with a continuous, autonomous architecture, the Agentic SOC.
The Current SOC Reality: The Burden of Manual Labour
The status quo is not merely inefficient. It is fragile. Most enterprise SOCs are constrained by three structural crises:
1. The Triage Crisis: Enterprise SOCs face thousands of alerts per day. Industry data indicates that nearly 78% of alerts are left uninvestigated or receive only cursory review due to sheer volume. This is not negligence; it is the predictable result of alert volume outpacing analyst capacity.
Over time, this creates a de facto “risk tolerance” shaped by capacity limits rather than strategy. Critical signals are buried under false positives, and detection fidelity degrades.
2. Fragmented Ecosystems: Security stacks have expanded into disconnected tools that do not share context. SIEM, EDR, Identity, Cloud, SaaS, analysts manually pivot across control planes to reconstruct narrative context.
Research shows 69% of organisations cite tool sprawl and visibility gaps as primary barriers to effectiveness. The telemetry exists, but correlation depends on human stitching. The cognitive load required to reconcile identity, endpoint, and cloud data manually creates blind spots where sophisticated attacks persist undetected.
3. Reactive Fatigue: The tiered model reinforces a culture of firefighting. Analysts spend cycles performing repetitive enrichment and log correlation rather than pursuing proactive threat hypotheses.
Burnout rises. Turnover accelerates. Skilled operators are reduced to clearing queues. Over time, the SOC becomes operationally busy yet strategically stagnant.
The Agentic Leap: From Linear Workflow to Continuous Reasoning
The transition to an Agentic SOC is not a tool upgrade. It is a structural redesign.
Instead of linear tiers and manual escalation, the SOC becomes a persistent reasoning system; a circular architecture where detection, investigation, and response operate continuously.
This shift rests on four foundational capabilities:
Persistent AI Agents
Static tools wait for input. Agents initiate enquiry.
Persistent agents continuously interrogate identity graphs, cloud control planes, endpoint telemetry, and configuration drift across environments. They autonomously query, enrich, and correlate data without requiring escalation chains to move an investigation forward.
They do not rely on human availability. They provide continuous vigilance, reducing the time between signal emergence and contextual understanding.
Reasoning Over Rules
Traditional automation depends on deterministic playbooks: if X, then Y. These scripts fail when adversaries introduce novel tradecraft.
Agentic SOCs incorporate reasoning engines powered by LLM-driven inference. Instead of matching predefined signatures alone, agents generate investigative hypotheses, test them against live telemetry, and adapt their path based on observed behaviour.
They evaluate intent and context, not just rules.
This allows the SOC to detect “living off the logic” attacks, identity abuse, and subtle lateral movement patterns that evade purely signature-based detection.
Continuous Enterprise Memory
Effective reasoning requires continuity.
Agentic architectures maintain a rolling contextual data window organised around users, assets, identities, and behaviours. Rather than investigating events in isolation, agents retain institutional memory across time horizons.
This eliminates siloed context and enables correlation between seemingly benign initial access and exploration activity observed weeks earlier and present anomalies, a critical capability for identifying advanced persistent threats.
Proactive Autonomy
In a tiered model, response begins after alert validation.
In an Agentic SOC, agents operate pre-emptively. They align observed behaviour directly to adversarial tradecraft frameworks such as MITRE ATT&CK, mapping tactics and techniques rather than relying solely on signatures.
Through behavioural analytics and adaptive fingerprinting, agents construct attack chains in near real-time, escalate only high-confidence incidents, and suppress noise at machine speed.
The human is no longer responsible for clearing alerts, but for overseeing system integrity.
Architectural Divergence: Current vs. Agentic SOC
This architectural redesign is not incremental. It redefines how security capacity scales.
Workflow
- Tiered SOC: Linear, handoff-driven, latency-prone.
- Agentic SOC: Circular, continuously sensing and reasoning, escalating only validated threats.
Detection Model
- Tiered SOC: Signature and rule-based; brittle against novel attacks.
- Agentic SOC: Behaviour and intent-based; adaptive through contextual reasoning.
Human Role
- Tiered SOC: Frontline triage and manual enrichment.
- Agentic SOC: Strategic oversight, governance, threat modelling, and validation of high-risk actions.
In the traditional model, scale is measured in headcount. In the agentic model, scale is measured in reasoning cycles per second.
The Leadership Pivot: Governing Compute
The Agentic SOC operating model demands executive-level reorientation.
The CISO’s mandate is no longer to expand analyst capacity to match alert volume. It is to govern intelligent systems capable of investigating at machine speed.
Security capacity becomes decoupled from hiring velocity.
By delegating the OODA loop — Observe, Orient, Decide, Act — to autonomous agents for many low and mid-complexity threats, organisations elevate human defenders into higher-value roles: governance, adversary strategy, resilience architecture, and oversight.
Autonomy does not eliminate humans. It reframes their leverage.
The Autonomy Readiness Assessment
Before dismissing this as theoretical, consider three questions:
-
Can your architecture detect, investigate, and contain a complex identity-based attack across cloud and on-premise systems in under 10 minutes, without manual correlation?
-
Can you investigate 100% of alerts with full contextual depth, or are you structurally forced to ignore “low-priority” signals where sophisticated attacks often hide?
-
Is your automation adaptive and reasoning-driven, or limited to brittle playbooks that fracture when threat vectors change and context shifts?
If the honest answer to these questions reveals latency, selective visibility, and fragile automation, the issue is not performance, it is architecture.
The tiered SOC was built for a world where human operators held the speed advantage.
That world no longer exists.
The decision now is not whether autonomy will define security operations. It is whether your SOC will be structured to govern it.
Loved this insight?
Share it with your network and help secure the digital world.